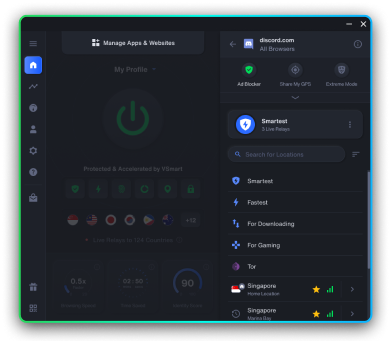
Bulletproof privacy in one click
Discover the world's #1 privacy solution




Coming soon

Coming soon

Coming soon



Chapter 14: IoT Hacks

Dive into the unsettling world of government-controlled GPS tracking!

Trash Talk: How your garbage can be exploited by hackers, law enforcement, and government agencies

It’s time to uncover how government surveillance gets personal.

Lifting the lid on the internet's most invasive tracking method: Browser fingerprinting.

The silent menace shaking the core of IT security

DuckDuckGo vs. Startpage: Which search engine reigns supreme for your online privacy?

Forget the tin foil hat myths, discover the very real and growing threat to your privacy: Laser Listening Systems

Think VPNs give you online anonymity? Think again.

Find out how governments are using satellites to spy on their own citizens.

Explore how your device's unique 'canvas fingerprint' is shaping the internet you see and how you can take back your privacy.

Discover the various ways that countries all over the world spy on citizens without any specific mandate.

Ever wondered how your data gets harvested online? We unmask the world of web scraping.

Hackers aren't the only ones who use botnets...

The Marketer's Hidden Weapon: How device fingerprinting knows you better than you might think...

Chapter 5: A history lesson and future look at how the government is destroying encryption.

Are you unknowingly revealing your digital identity? Learn how browser extensions can make you stand out in the crowd!

Chapter 4 - Social Media Analysis. Find out how your social media sharing is feeding right into government mass surveillance machine.

Virtual Machines: Not just for techies! Discover how VMs can safeguard your online privacy.

Meta and Facebook phishing scams take a dark turn. Learn about the latest tricks being used, and the damage they cause.

Unstoppable domains are popular with the tech-savvy. But are these crypto domains the real deal?
Discover how SOCKS5 proxies can safeguard your online identity and why they're a game-changer for privacy enthusiasts.

Get ready to explore the truth, one chapter at a time.

Warning: Getting caught out by one of these Instagram phishing scams could cost you more than just your paycheck!
Want evidence that device and browser fingerprinting are dangerous? Hold onto your hats, we're getting technical.

Get the lo-down on data brokers. What are they, how do they operate, and how to protect your valuable personal data and online privacy.

Discover the world's worst internet freedom offenders - Is your country on the list?

Third party browser cookies in Chrome are being banned. But what about Browser fingerprinting
Do you know the difference between a VPN and a proxy? Which is faster, more secure, or better for streaming?

Keep your financial secrets safe! Learn about anonymous payments and how they can shield you from identity theft and unwanted surveillance.

Big tech censorship has nothing to do with conspiracy theory. It's about global policies that hurt millions of people.

Worried about Google spying? You let them control your E-mail, monitor your videos, and you invite them into your home

Staying connected and sharing life has a price: privacy. Find out which social media apps are the most data-hungry and what you can do about it.

Type in a bunch of numbers, get a domain name? Why is that useful?! Reverse DNS is more important than you think.

Learn about how one of the most popular Twitch ad blockers was leaking IDs to Russia, and the alternatives you can use.

Don't game in the dark! 10 must-know tips to protect your privacy online

Browser fingerprinting is like internet tracking on crack. It's highly invasive and impossible to block even with a VPN or Tor.
Looking for new reading material? Unleash your inner privacy pro with this reading list on online security!

Find out which encrypted chat app is best at stopping surveillance and safeguarding your privacy.

Privacy Under Attack: How Mass Surveillance Threatens Your Freedom

Do you know what information your IP address reveals? It could be enough to put your privacy at risk.

The first days after getting hacked can be life or death for a company. Learn the steps to take if you want to survive.

From clicks to data: Understanding the secrets of your digital footprint!

Wearable fitness trackers can keep you healthy but are they keeping you safe? Discover how your fitness tracker data could be putting your privacy at risk.

Slow speeds, constant disconnections, zero-log lies, and so much more. We take a look at the disadvantages of VPNs and explore a better alternative.

Discover everything you need to know about the Pegasus spyware silencing journalists and activists around the globe.

Did you know your Alexa voice recordings are kept FOREVER? Here a few other reasons why you'll want to delete Alexa recordings.

Is WhatsApp safe to use? Delve into WhatsApp privacy features, policies, and practices to find out how safe your data is.

Digital Privacy: Why you should care and how to ensure it!

LinkedIn is one of the easiest ways to get doxxed, harassed, and stalked. Learn to protect your LinkedIn privacy!

Biometric data: the new frontier of identity verification or a threat to your personal privacy?

Discover how top privacy coins like Monero, Zcash, and Dash can protect your identity and information while using cryptocurrencies.

Every keystroke you make, every keystroke you take, is someone watching you? Discover the dangers of keylogging software and how to protect against it.

Discover the best whistleblower movies and the real-life characters and events that inspired them.
Discover the famous whistleblowers who risked everything to expose corruption and wrongdoing in some of the most powerful organizations in the world.

Discover YouTube's incognito mode and keep your viewing history hidden.

If TikTok's data harvesting and spying concerns leave you wondering how to delete Tik Tok, we've got you covered.

The use of facial recognition technology is spreading. Here are just five reasons why it should be stopped!

Get the popcorn ready for a surveillance movie marathon! Here are the Hoody top 10 movies about privacy and surveillance.

Big Brother has more than one eye...check out the countries that have joined forces to spy on you through mass surveillance.

Employee monitoring "productivity software" is just spyware dressed in a suit. It's a massive invasion of privacy yet bossware is perfectly legal. Learn more.

Never see the "Sorry, this content is not available in your location" message ever again! Access all areas with our guide to bypassing geo-blocks.

No one loves an oversharer...apart from cyber criminals! Here are 6 things you should never share on your social media account.

Is your ad blocker doing more harm than good? Find out more here, plus, what you can use instead!

Traveling to any of these 15 countries? Your VPN could land you in jail. But Hoody has your back.

Government tracks the VPN users activity through ISP backdoors and none of your data is safe as claimed. Shocked? Know how it is done.

Twitch ads are annoying. Here are the best ways to block them, and some of them even help the streamer you're watching!
So you've come to realize that most VPN claims are overinflated. Ready to move on? Here's the best VPN alternative.

If you're not worried about your online privacy yet, you should be. Don't believe us? Here are 11 internet privacy quotes to prove it.

You think your VPN is trustworthy because they're audited? Think again. Learn how easy it is to get fake VPN audits.

Oops, they did it again! Yet another Twitter data breach. Let's look at the latest Twitter hacked headline and the past lessons Twitter has failed to learn from.

We know the dangers of online tracking. But these stories show how browser fingerprinting ruins lives.

If you don't know how you're being tracked, how can you stop it? Read this browser fingerprinting guide for the clueless.

What happens when the major advertising authorities take a stand against browser fingerprinting? Chaos.

Your personal data has made Mark Zuckerberg a centi-billionaire. Here's how and what you can do about it.

Russia made SORM-3 surveillance the law! Learn how Russian VPNs leak all of your information to the government.

Five Eyes produced one of the most frightening spyware apps on the planet: Xkeyscore. Learn what they already know.

Spear phishing is one of the most highly targeted, and successful, hacks in recent years. Learn to defend yourself!

Is the current version of the Torrentz search engine the same as the original? Can it be trusted? Dive into the history.

Can someone impersonate you and implicate you of a crime by cloning your web browser's fingerprint? Find out here!

Not all DNS servers are the same! Learn how to rate DNS servers, install a new one, and do a DNS flush on the old one.

A new fingerprinting hack has compromised the privacy oriented Tor browser! Learn how you can avoid being tracked.

Sometimes, you need to dig around under the hood. This guide will show you how to get into and use Windows 10 Safe Mode.

An article about the Anonymous hacker group. Topics covered include who is Anonymous, where the Anonymous hackers originated, a history of their exploits, the privacy issues that led to several arrests of Anonymous members, and current Anonymous activites.

Don't know how the Internet really works? Discover the basis as we answer the question: What is an IP address?

Device fingerprinting over Bluetooth can track you… even through a VPN! Check out the insecure side of Bluetooth.
Discover the world's #1 privacy solution
Coming soon
Coming soon
Coming soon