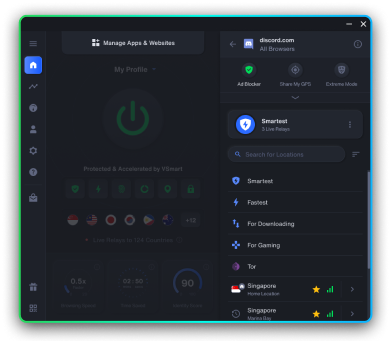
Bulletproof privacy in one click
Discover the world's #1 privacy solution




Coming soon

Coming soon

Coming soon



Chapter 14: IoT Hacks

Dive into the unsettling world of government-controlled GPS tracking!

Trash Talk: How your garbage can be exploited by hackers, law enforcement, and government agencies

It’s time to uncover how government surveillance gets personal.

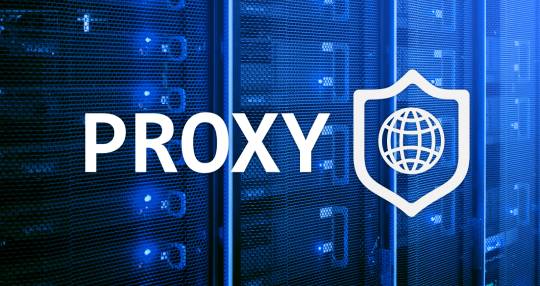
Lifting the lid on the internet's most invasive tracking method: Browser fingerprinting.

The silent menace shaking the core of IT security

DuckDuckGo vs. Startpage: Which search engine reigns supreme for your online privacy?

Forget the tin foil hat myths, discover the very real and growing threat to your privacy: Laser Listening Systems

Think VPNs give you online anonymity? Think again.

Find out how governments are using satellites to spy on their own citizens.

Explore how your device's unique 'canvas fingerprint' is shaping the internet you see and how you can take back your privacy.

Discover the various ways that countries all over the world spy on citizens without any specific mandate.

Ever wondered how your data gets harvested online? We unmask the world of web scraping.

Hackers aren't the only ones who use botnets...

The Marketer's Hidden Weapon: How device fingerprinting knows you better than you might think...

Chapter 5: A history lesson and future look at how the government is destroying encryption.

Are you unknowingly revealing your digital identity? Learn how browser extensions can make you stand out in the crowd!

Chapter 4 - Social Media Analysis. Find out how your social media sharing is feeding right into government mass surveillance machine.

Virtual Machines: Not just for techies! Discover how VMs can safeguard your online privacy.
Discover how SOCKS5 proxies can safeguard your online identity and why they're a game-changer for privacy enthusiasts.

Get ready to explore the truth, one chapter at a time.
Want evidence that device and browser fingerprinting are dangerous? Hold onto your hats, we're getting technical.

Get the lo-down on data brokers. What are they, how do they operate, and how to protect your valuable personal data and online privacy.

Discover the world's worst internet freedom offenders - Is your country on the list?

Big tech censorship has nothing to do with conspiracy theory. It's about global policies that hurt millions of people.

Staying connected and sharing life has a price: privacy. Find out which social media apps are the most data-hungry and what you can do about it.

Don't game in the dark! 10 must-know tips to protect your privacy online

Browser fingerprinting is like internet tracking on crack. It's highly invasive and impossible to block even with a VPN or Tor.
Looking for new reading material? Unleash your inner privacy pro with this reading list on online security!

Find out which encrypted chat app is best at stopping surveillance and safeguarding your privacy.

Privacy Under Attack: How Mass Surveillance Threatens Your Freedom

Do you know what information your IP address reveals? It could be enough to put your privacy at risk.
Discover the world's #1 privacy solution
Coming soon
Coming soon
Coming soon